Service Level Agreement
Cloud server hosting from Port Cities meets the toughest criteria for a safe & reliable hosting of your ERP system.
99.9% uptime guarantee
We work with different hosting providers worldwide that always deliver at least 99.9% uptime guarantee. The uptime guarantee comes directly from the hosting provider and excludes any planned maintenance windows.
Initial Odoo installation & set up
We install Odoo and the related monitoring tools to your server. It also includes installing the mail server, setting up the database backups, setting up high availability, and setting up the antivirus software. We also configure the firewall settings.
Server monitoring 24/7
whole year
We monitor what is happening on your server constantly. We keep your server updated & regularly check its functions as well as utilization of disk, RAM, CPU. A system of alerts is in place to keep us informed about any activity on your server, 24/7.
Standard Server Maintenance
Server maintenance aims to ensure that the system itself continues to function as required. It includes the following tasks:
-
Verify backups are working
We perform an automated check to ensure that backups are working. To accomplish this we include an alert in the actual backup script that alerts our staff when a backup has failed to save to the target destination. -
Check disk usage
If disk usage is exceeding 90% of disk capacity, our alerts will inform us and we will contact the customer to recommend to either reduce usage or add more storage. If Port Cities needs to delete something, they will get explicit approval from the customer in this situation. -
Monitor Server Alarms and warnings
We set up alerts and warnings on the server and these alerts are sent directly to our 24/7/365 on call server support staff. Our server support staff take action on these alerts as described above in the server emergency alerts section making sure that the customers operations continue to function as normal. -
Update OS Patches
Updates for Redhat/Linux/Ubuntu systems are released frequently. Hackers often scan for vulnerable systems within hours of an issue being disclosed. So rapid response is key. -
Update the Server Monitoring and Emergency Alerting Tools
If there are any updates to the Server Monitoring and Emergency Alerting tools, Port Cities will get approval from the customer before applying these updates. -
Check server utilization
We have automatic checks to let us know when server resources are approaching critical levels. We work with the customer and if they are nearing limits, we recommend when they need to plan on adding resources to their server. Please note that this does not include server software performance tuning which is different. -
Review user accounts
Standard security needs call for server side account to be promptly removed when the user no longer require it for his/her duty. Port Cities will remove the server account on the last day that the employee is with our organization. -
Change server passwords
We routinely change server side passwords used for maintenance/support every 6 to 12 months. -
Check system security
Annually, we review the server’s security using a remote auditing tool. This security audits serves as a check on system configuration, OS updates and other potential security risks.
Server Emergency Alerts
Our server support team utilizes server monitoring software to routinely check the server and instance/database. We set up emergency notifications to notify/page our 24/7/365 on-call server staff of a critical situation including:
-
Server disk space is above the 90% threshold
We notify the customer. -
The Server is currently down
We will attempt to restart the server. -
Odoo/Web Server is currently down
We will attempt to restart the server. -
The Instance/Database is currently down
We will attempt to restart the server. -
Database connections are approaching the maximum amount as defined in the postgresql configuration file for the database
We notify the customer. -
A Database backup has failed to save to the target destination
If the issue is due to disk space, we notify the customer. -
Virus has been detected on the server
We take the quarantine action recommended. -
Security patch needs to be applied on the server
We schedule to apply the security patch.
Scheduled Server Health & Performance Checking
Our server team continually has the server health & performance tools running on the server. We perform a weekly review of the health & performance to ensure that the client is meeting optimal levels. If needed, we coordinate with the customer on what we feel will improve the servers health & performance.
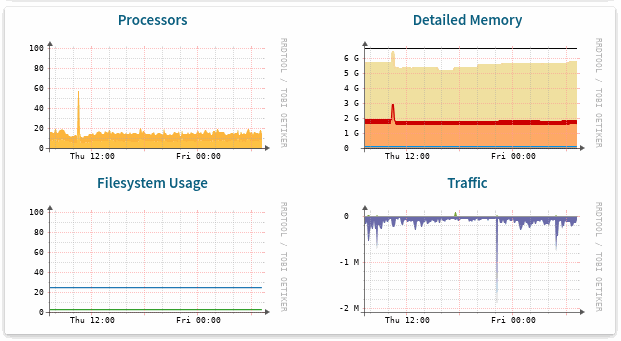
Customer Access to their Server Graphs
For dedicated production server customers, we offer them the ability to access their own server graphs through a website with a username and password provided by us. The offer is quite extensive with processor, memory, disk, postgres graphs all available for customers to view.
Here is an example of some graphs offered:
Standard Network Based Security Maintenance
This security is provided on the network level and includes secure network configurations, frequent network scans, and overall knowledge of maintaining a secure network.
Firewall Protection Maintenance
Firewalls increase security and, when properly configured, will prevent certain disasters from occurring. With this service our administrators will configure and maintain a firewalled routing perimeter for the server in question.
Patch Management & Security Updates
Port Cities implements automatic operating system updates and patches as part of our routine procedures. This will be a part of a continuous maintenance period of updates that take place regularly. As new kernels, security patches, service packs, and hot fixes are released the servers will be updated automatically.
DDoS Protection
DDoS is defined as protection from Distributed Denial of Service (DDoS) attack. All hosting providers used by Port Cities have very large network capacities and have designed their infrastructure to withstand the largest Distributed Denial of Service (DDoS) attacks. Their automatic and manual mitigation systems can detect and divert attack traffic at the edge of their multi-continental networks, before it gets the chance to disrupt service availability.
Brute Force Protection
Brute Force protection is defined as protection from trial-and-error methods used to obtain information such as a user password. Firewalls and intrusion prevention systems on servers help detect and block threats such as brute-force password attacks.
Virus, Malware & Ransomware protection software
Port Cities has software that is installed on the server to scan for security threats such as Viruses, Malware, and Ransomware.
Grade A Web Security utilizing SSL
All web connections to client instances are protected with 256-bit SSL encryption (HTTPS with a 2048-bit modulus SSL certificate), and running behind Grade A SSL stacks. All our certificate chains are using SHA-2 already.
Odoo Initial Setup & Configuration
This task encompasses installing Odoo on the server and the related monitoring tools for the server. It also includes installing the mail server, setting up the database backups, setting up high availability, and setting up the antivirus software. We also configure the firewall settings.
High availability
Each customer database is replicated in real-time on redundant storage located in the same data center, so a failover can happen quickly in case of hardware failure, with no data loss.
Managed database backups
This is the schedule of backups of the customer’s production environment.
We provide:
- 14 full backups up to 3 months: 1/day for 7 days, 1/week for 4 weeks, 1/month for 3 months.
- Users can download manual backups of their live data at any time.
- Customers can contact our server support helpdesk ([email protected]) to restore any of the backups we keep or a live backup the customer has taken to the live database.
Number of Servers Database Backups Replicated to
The Database Backup replication across different servers depends on the Server Management support level you have opted for.
This SLA does not cover:
- Server software support or server software issue remediation
- Server hosting provider
- Client manages their own server or domain
- Client's local area network
- Client-provided Internet connectivity or end-user software
- Entities inside Client's internal network including, but not limited to, firewall configuration and bandwidth shaping, local area workstations, or other servers, equipment, and software that have a potential bearing on the local networking environment
- Any predetermined Scheduled Service Downtime
Any interruptions, delays or failures caused by Client or Client's employees, agents, or subcontractors, such as, but not limited to, the following:
- Inaccurate configuration
-
Any problems related to attacks on the machine such as hacking, bandwidth-based attacks of any nature, and service or operating system exploits
-
If the client requests SSH access to their server, Port Cities cannot guarantee the safety of any data on the server or backups. Port Cities will not be responsible for any data loss in this situation.
-
Client initiated server over-utilization.
- Non-compliant use of any software installed on the server
Port Cities is not responsible for hardware failures from hosting providers that result in a loss of data. If hardware failure is experienced and subsequent data loss occurs, client is ultimately responsible for data lost after the most recent backup. Port Cities shall not be liable for loss of data after the most recent backup under any circumstances.
Database Backups
Port Cities keeps 14 full backups of each Odoo database for up to 3 months: 1 per day for 7 days, 1 per week for 4 weeks, 1 per month for 3 months. Backups are replicated across a number of servers defined by the service management support level that you have chosen. Users can download manual backups of their live data at any time, and Customers can contact our helpdesk to restore any of the backups we keep or a live backup the customer has taken to the live database
Database Security
Customer data is stored in a dedicated way - no sharing of data between clients is possible. Data access control rules implement complete isolation between customer databases running on the same cluster, no access is possible from one database to another.
System Security
All Port Cities servers are running hardened Ubuntu/Linux distributions with up-to-date security patches. Installations are ad-hoc and minimal to limit the number of services that could contain vulnerabilities (no PHP/MySQL stack for example).Only a few trusted Port cities engineers have clearance to remotely manage the servers - and access is only possible using SSH key pairs (password authentication disallowed).
Staff access
Port Cities helpdesk staff may sign into your database to access settings related to your support issue. For this they use their own special staff credentials, not your password (which they have no way to know). This special staff access improves efficiency and security: they can immediately reproduce the problem you are seeing, you never need to share your password, and we can audit and control staff actions separately! Our helpdesk staff strives to respect your privacy as much as possible, and only access files and settings needed to diagnose and resolve your issue.
Communications
All web connections to client instances are protected with state-of-the-art 256-bit SSL encryption. Our servers are kept under a strict security watch, and always patched against the latest SSL vulnerabilities, enjoying Grade A SSL ratings at all times. All our SSL certificates use robust 2048-bit modulus with full SHA-2 certificates chains.
Credit Card Safety
We never store credit card information on our own systems. Your credit card information is always transmitted securely directly between you and our PCI-Compliant payment acquirers.
Password security
Customer passwords are protected with industry-standard PBKDF2+SHA512 encryption (salted + stretched for thousands of rounds). Port Cities staff does not have access to your password, and cannot retrieve it for you, the only option if you lose it is to reset it. Login credentials are always transmitted securely over HTTPS. As of Odoo 12.0, customer database administrators even have the option to configure the rate limiting and cooldown duration for repeated login attempts. Password policies: as of Odoo 12 database administrators have a built-in setting for enforcing a minimum user password length. For older versions it is possible to achieve the same effect through customization. Other password policies like required character classes are not supported by default because they have been proven counter-productive - see e.g. [Shay et al. 2016]).
Network defense
All data center providers used by Port Cities have very large network capacities, and have designed their infrastructure to withstand the largest Distributed Denial of Service (DDoS) attacks. Their automatic and manual mitigation systems can detect and divert attack traffic at the edge of their multi-continental networks, before it gets the chance to disrupt service availability. Firewalls and intrusion prevention systems on Port Cities Cloud servers help detect and block threats such as brute-force password attacks. As of Odoo 12.0, customer database administrators even have the option to configure the rate limiting and cooldown duration for repeated login attempts.